.NET - Generating Encrypted User Passwords
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
What is this about?
When I first started learning Canvas, I thought it was very convenient that I could create a new user and Canvas would automatically send an invitation to the new user with a link to the login page. What a great feature!
Once the decision was made to get on board, I started working on integration with the SIS, and quickly learned that when you import new users into Canvas, the SIS import process does NOT send out invitations, and no default passwords are assigned. So how were we going to notify new users that their account had been created? We came up with our own automated workflow process to watch for useres who had not yet been created in Canvas, and import those users with a temporary password.
At first, we were importing the passwords in clear text. Canvas later announced that the import would accept an encrypted password, which is a much more secure format, and I began working on adding this functionality to our existing workflow service.
I will share a .NET project that includes a class that will encrypt and verify signatures in the format recognized by Canvas. If you are using .NET and interested in encrypting your passwords, you should be able to implement this class in your projects. This class is applicable beyond Canvas user passwords to encrypt data in general and may be useful in other ways.
Why am I generating passwords anyway?
I am working with an institution that does not have a single-sign-on solution implemented. We are depending on the built-in Canvas login to gain access to the platform.
References
There are a few basics that would help to understand when working with the associated project:
- Working knowledge of C#:
- The Microsoft encryption name space:
- Canvas article on SSHA password:
- SSHA Password Generation
- As mentioned in this article, it was very helpful to work through the Python script, as there was a string conversion that was being done that I was not doing initially, it made all the difference:
- Download the source code for this demo app here:
- Download the sample user import file attached to this post: user-password-import-test.csv
What I Learned...
When putting my class together, I used other references and examples, which are documented in the code.
The ComputeHash() method returns an array of 20 bytes, every time.
This is standard in each example I worked through, but it wasn't working for Canvas.
This was created some time ago, but I would like to thank @tfullwood for pointing answering questions at the time and directing me to the Python script. Working my way through that script helped me identify a step that I was leaving out: converting the 20 byte array to a 40 byte array.
In my class clsPasswordGen, you will see two versions of the methods to generate and validate the hashed password:
- generateSaltedPassword() and complimentary verifySaltedPassword()
- generateCanvasSaltedPassword() and compliment verifyCanvasSaltedPassword()
You will see an extra step in the Canvas method: ToHexString(), this is where the 20 byte array is converted to a 40 byte array.
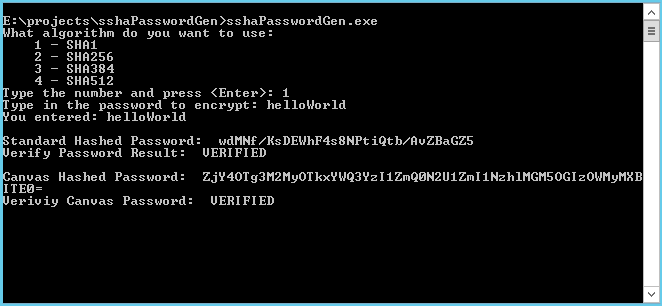
Using the test app associated with this post to hash the password "helloWorld", a standard SSHA hash will generate something like this:
- wdMNf/KsDEWhF4s8NPtiQtb/AvZBaGZ5
Hashing the same password for Canvas compatibility will generate something similar, but of greater length, like this:
- ZjY4OTg3M2MyOTkxYWQ3YzI1ZmQ0N2U1ZmI1NzhlMGM5OGIzOWMyMXBITE0=
The test app will output both versions of the result.
Attached to this post is a sample user import file, "user-password-import-test.csv", with the password listed above (helloWorld). Import the file to your test environment and login with the password "helloWorld", and it will work. Then generate your own password, update the import file and try again to validate your generated password hash works.
How to use the test app
Download the source code from BitBucket here: sshaPasswordGen source code
Compile the code and run the executable from the command line.
You will be prompted to select an encryption algorithm (you want option 1 for Canvas: SHA1).
You will be prompted to type in the password to encrypt.
The results will be displayed.
This is a very simple test app to demonstrate how to implement the encryption class.
You will notice there are several encryption algorithms implemented, I left them in place for demo and testing purposes.
This encryption class can be used for purposes other than Canvas passwords.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.