JWS signature invalid
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am trying to use the Assignment and Grade Services in a tool and am stuck on retrieving an access token. I am following the instructions here to make a post request to /login/oauth2/token with a grant_type of client_credentials.
Here is the information contained in the body of the post request:
{'scope': 'https://purl.imsglobal.org/spec/lti-ags/lineitem https://purl.imsglobal.org/spec/lti-ags/result/read',
'grant_type': 'client_credentials',
'client_assertion': u'eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiIxMDAwMDAwMDAwMTUyOCIsImlzcyI6Imh0dHA6Ly9sb2NhbGhvc3Q6NTAwMC8iLCJqdGkiOiIxMjM0NTY3ODkwOTg3NjU0MzIxIiwiZXhwIjoxNTk4ODkyOTA4LjkyNjA0OSwiaWF0IjoxNTk4ODg5MzA4LjkyNjA0OSwiYXVkIjoiaHR0cHM6Ly93aWxleS5pbnN0cnVjdHVyZS5jb20vbG9naW4vb2F1dGgyL3Rva2VuIn0.NZOjZ-i-s7HvTiOL-wv50ptPIAiR10RyhaAksmLFqAEjPP0T1cO8TdDR0NXBkV5IupyLzW5Cm8AUgucz_LPyjbLwK48ZCbWqo6Z7_LabpQlzW4clqDh6V4DEBwl8pmRSsLrvNTCJHIQwiTbXFpRR0rGCtSQXAhNbvxh6GqL_HE1WJA2MaBLWtHdYKwMruHlSeEVIvCfb-g0Mw6XnmEodKkhAqO8c29LgZRmL80qSBImNrbLbWx7-DltV4Me-OeqUs_3hWUtzoTGTu2P7G8Wu6we-Hio45Qv9YIK-vcr6YYJO3JInxcUdF5b6cLrScEWQHyCn8c6fUUlMBjJPfiu6tQ',
'client_assertion_type': 'urn:ietf:params:oauth:client-assertion-type:jwt-bearer'}Decoded JWT:
{
"sub": "10000000001528",
"iss": "http://localhost:5000/",
"jti": "1234567890987654321",
"exp": 1598892908.926049,
"iat": 1598889308.926049,
"aud": "https://wiley.instructure.com/login/oauth2/token"
}Using the following public key, I can verify that the signature for the jwt in the client_assertion field is valid by entering it into jwt.io.
-----BEGIN PUBLIC KEY-----
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAr2kl1OwVx3D6UHFmnVoZ
++9hWqp+c6Fg1mLMLJOIRKIGzh/nzLtbTQm+8+ilY05hHke9P+VO3i2Okece/JkC
u9LbJWIIgi4sSPX0ZKgVmTt7rnSEYeg0hRqj1W2NDIyXf91c4jLQH0FbWSd70h50
3z1Q3AxcnUNkjuYP+5wsPhKoGT9Uk6I6aZUvDNlv+0Bm9/caqJDtYUASLZT/DlrE
M3dkTCsgdJxW45oCF5cwfNQHV8gAMH0u3+KGxPBnO9WfR4UEKh+JD7iY70b0y3vO
pMJFTWOZK1sZ7B0PppEId1zuxNT5arXMftSoJKnyoI6d3MgkRz2e2KO58AbbQK3p
oQIDAQAB
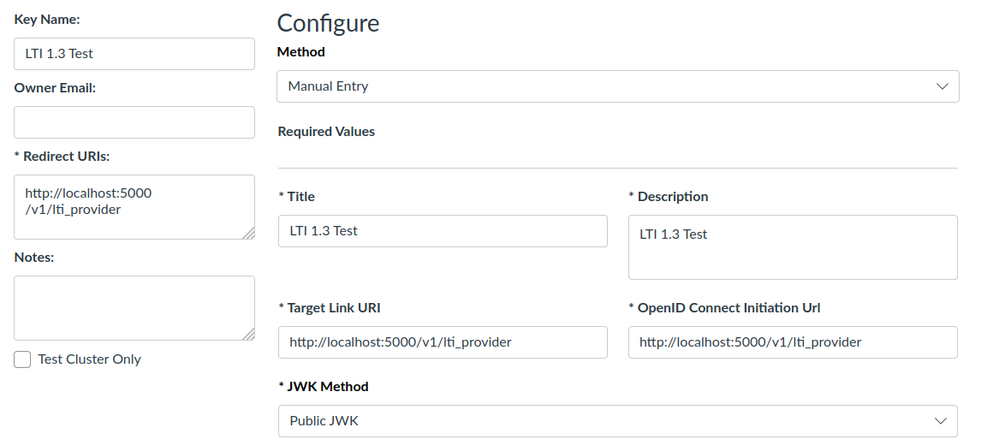
-----END PUBLIC KEY-----The LTI tool is configured as follows:
In the Public JWK field I have the following:
{
"e": "AQAB",
"n": "MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAr2kl1OwVx3D6UHFmnVoZ++9hWqp+c6Fg1mLMLJOIRKIGzh/nzLtbTQm+8+ilY05hHke9P+VO3i2Okece/JkCu9LbJWIIgi4sSPX0ZKgVmTt7rnSEYeg0hRqj1W2NDIyXf91c4jLQH0FbWSd70h503z1Q3AxcnUNkjuYP+5wsPhKoGT9Uk6I6aZUvDNlv+0Bm9/caqJDtYUASLZT/DlrEM3dkTCsgdJxW45oCF5cwfNQHV8gAMH0u3+KGxPBnO9WfR4UEKh+JD7iY70b0y3vOpMJFTWOZK1sZ7B0PppEId1zuxNT5arXMftSoJKnyoI6d3MgkRz2e2KO58AbbQK3poQIDAQAB",
"alg": "RS256",
"kid": "10000000001528",
"kty": "RSA",
"use": "sig"
}And under LTI Advantage Services I have enabled all permissions.
I am stumped why this is not working. When I make the post request to https://<mydomain>/login/oauth2/token all I receive is this:
{"error":"invalid_request","error_description":"JWS signature invalid."}But the signature is valid.
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I merely converted the PEM format into JWKS format using PHP code.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I also had this error, but my LTI was working through D2L and Blackboard. Turns out if you're using a "Public JWK URL", Canvas expects the URL result's content-type header to be "application/json".